WHAT IS
The Dull Platform
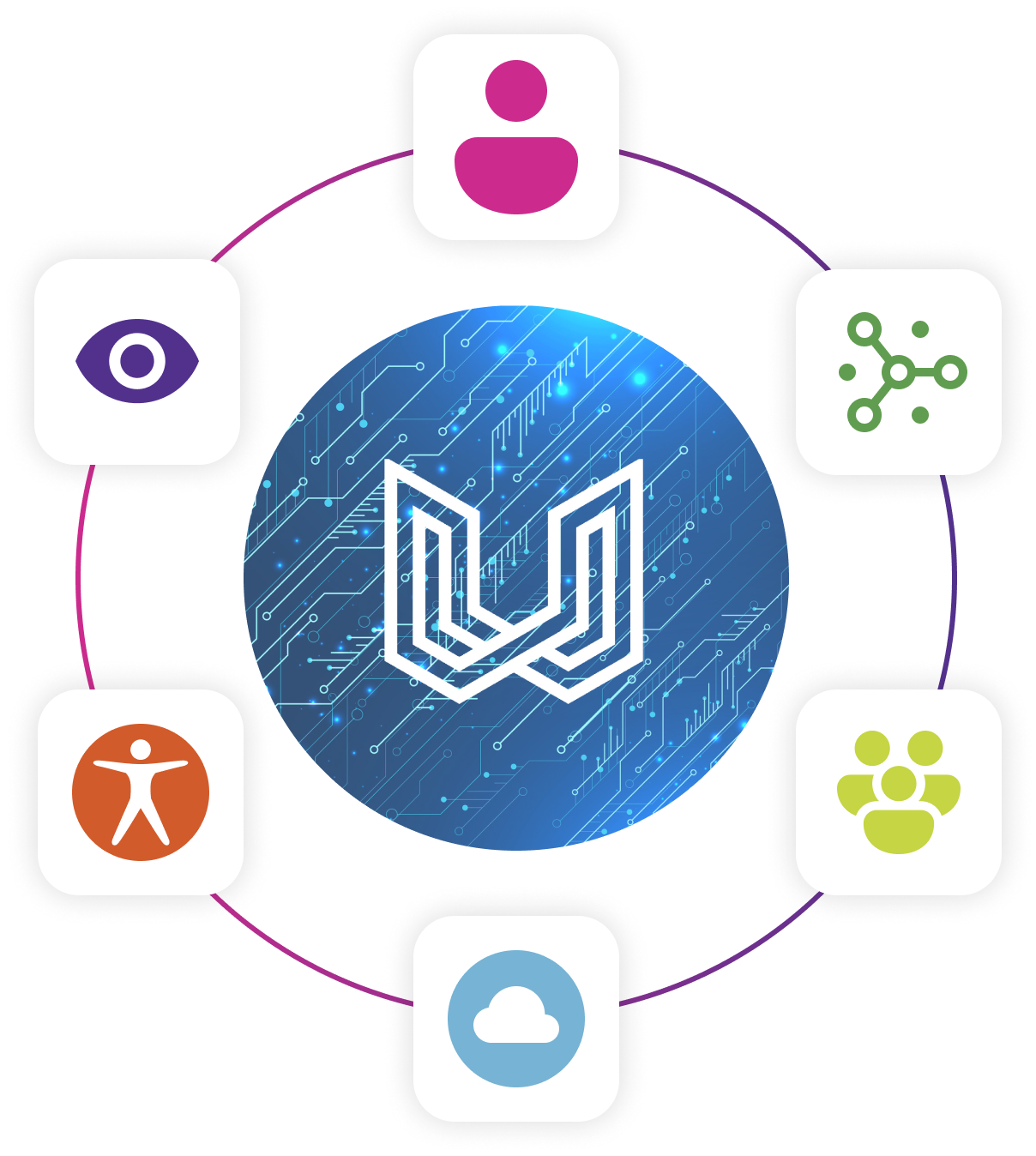
The Dull Platform uses MicronetworkingTM which creates a Secure Access Fabric that controls access to data sources, systems and devices. Uniquely this can be deployed across multiple organisations in a collaborative way. The Dull Platform provides unprecedented flexibility and control, along with providing visibility of who is doing what and when.
WHAT IS
The Problem the Dull Platform can help you with
When working with partners, vendors, and clients, it can be hard to establish quick and easy access to devices, systems, and data sources. This becomes even more difficult across multiple organisations, as different technologies and organisational policies can get in the way. Managing this complexity is only part of the challenge. As these environments take away critical time from your people, which increases your operational costs and reduces your ability to respond quickly to changing business needs, halting innovation and growth.

HOW CAN
The Dull Platform Help You

The Dull Platform does not replace your existing networks, firewalls, or security policy, it works with what you have today. The Dull Platform adds an extra dimension creating secure network access with a Zero Trust posture, over the top of the networks and firewalls you have today.
The Dull Platform provides software-based control of your Network Access. Your control and configuration of Network Access is in plain English level of configuration and is separated from the encrypted tunnels the Dull Platform creates
The Dull Platform provides distributed control and visibility of the secure access between organisations. Allowing you to create secure access for a range of use cases.
The Dull Platform being independent of your current network and firewall setup, lets you securely setup and take down network access in minutes. This ease of creating secure network access allows you to open your perimeter to only approved devices, and reducers the complexity in ensuring only the right devices are getting access to the right data sources.
The Dull Platform’s Access Coordination enables secure network collaboration within and between organisations.
Access Coordination provides a critical capability that allows the Dull Platform’s Secure Access Fabric to be extended across multiple organisations.
The
Capabilities
- Zero trust security posture: Dull’s Secure Access Fabric enables a Zero Trust security posture including a “least privileged access” method of access and no connections being permitted before approval has been given. This approach acts as a mitigating factor against cyber threats.
- Software-defined & cloud delivered: Dull’s Secure Access Fabric is software-defined and cloud delivered and is easily deployable without the need for additional hardware or centralised gateways. This is a key tool in enabling secure anywhere and anytime access to digital capabilities.
- Visibility and Control: The Dull Platform lets you maintain control of access and visibility of all sessions managed by it via Session Event Logging, making all sessions auditable.
- Granular access control: Because we manage encryption and compliance down to the level of each connection, you have visibility of what is happening over each connection.
- Segmented control zones: Distributed architecture, segmented zones of control and de-centralised control of those segments mitigate against single points of failure.
- Access Coordination: This unique capability allows multiple organisations to collaborate efficiently and securely with each organisation being able to maintain granular control over their part of the network
Benefits of
The Dull Platform
Simplify management of network access and increase operational efficiency
Increase visibility of who does what and when
Realise operational efficiency and capability gains which can materially reduce cost and provide capability that is very expensive to achieve in any other way
Open up a new world of secure network access collaboration.
Bring order to access, using your existing infrastructure
Contact Us
Get In Touch With Us
If you are searching for a proven way to accelerate your business and reach the pinnacle of your niche, contact us at iCT Group. We would be pleased to discuss your business’s needs and goals for the future, and create a strategy to get you there.

